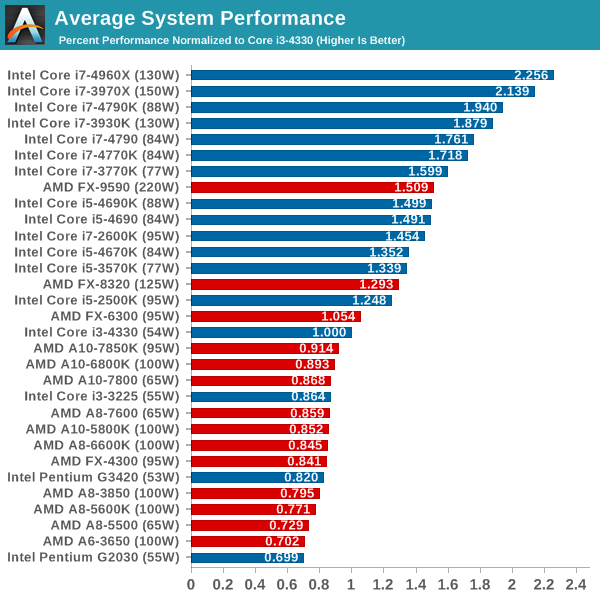
cpu chart 2015
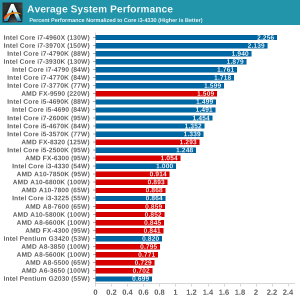
Unfortunately, many of the previously available options don’t work. Regardless of the host name, there are only two configuration options, windows and intervals. To run the Vapor in release mode, you want to increase execution. Furthermore, the SBT configuration is far more concise than Maven based on XML. On the desktop, it has components for creating scripts that meet Hollywood standards. The addition of several processing cores has continued to improve chip performance for more than a decade.
For the most part, processors have become the most important part of computers developed for editing. The main reason is because you have a 32-bit processor, which requires a 32-bit operating system. Furthermore, if the essence of the calculation changes over time, the chip can be reconfigured with new software designed to produce a new workload better.
The approximate code used in the test can be found on Github here. The complete source code is available here. You can have all the codes available on Github. JavaScript has many intrinsic properties which make it a fantastic choice for data science.
This graph shows the Fermi architecture. Google spreadsheets are completely free. The driving model is like the Maven archetype. The vector has been explained in more information in previous technology posts. This only requires the local browser and PCP installed on the host that you want to monitor.
To get started, it’s important to understand the making of the processor so that you understand what you receive. The prototype is a rather simple data model. Depending on the environment, additional packages or permits may be needed to carry out the test. The benchmark takes a few moments to complete, the operating system can adjust the CPU frequency if there is no user activity for a certain period.
You will have everything you need to manage benchmarks. The downside is that it is harder to find patterns over time, which can be more evident in tools like vmstat and pidstat, which offer smooth output.Frame speed is in single digits without sound, so it’s not really a valid platform at this time. In the wire, push the same amount of current wire to increase resistance (and extra heat) compared to the larger wire. Given the cost of about 78 times the price of GeForce, it can be said that the cost is not feasible.
If you manage a mass platform, CPU resources can be removed by getting and acting en masse. The framework that we will use for benchmarking is JMH. In the most frequent example, write your application in the cloud and develop it with it. When building real applications, there are many aspects to consider, so I made a complete benchmark between the most popular frameworks and technologies. So suppose you scroll through an application on your mobile. So, suppose you are experimenting with an email application.
cpu chart 2015
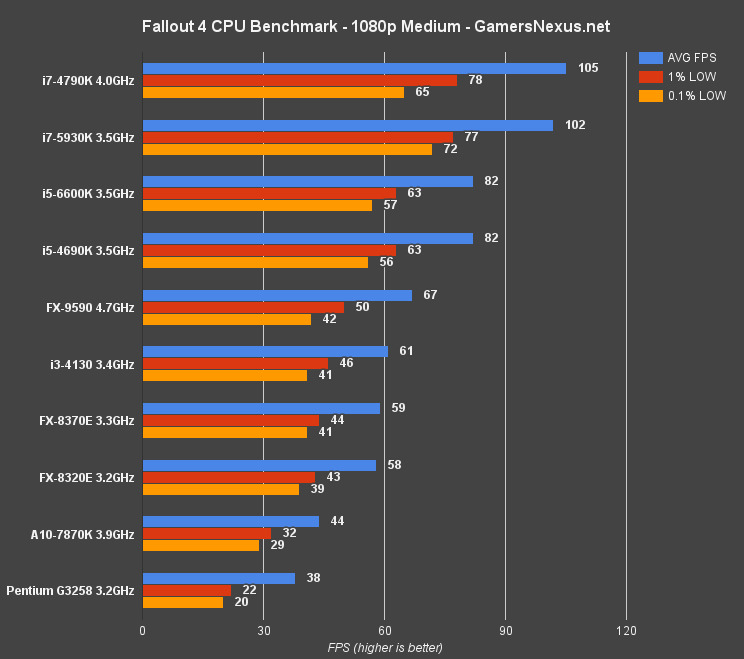
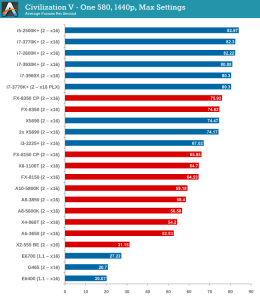
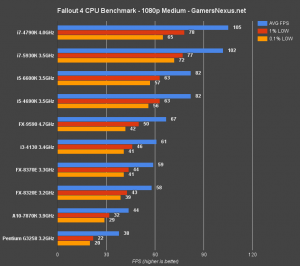
Fallout 4 CPU Benchmark: Major Impact on Performance i3, i5, i7
cpu chart 2015
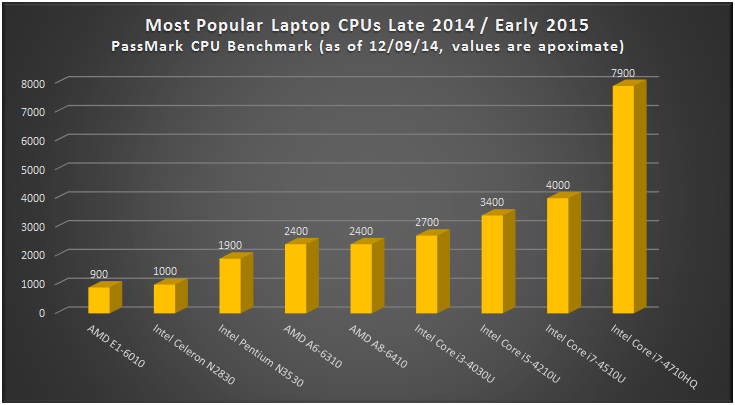
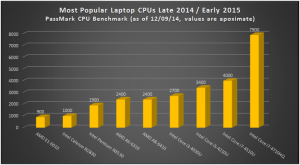
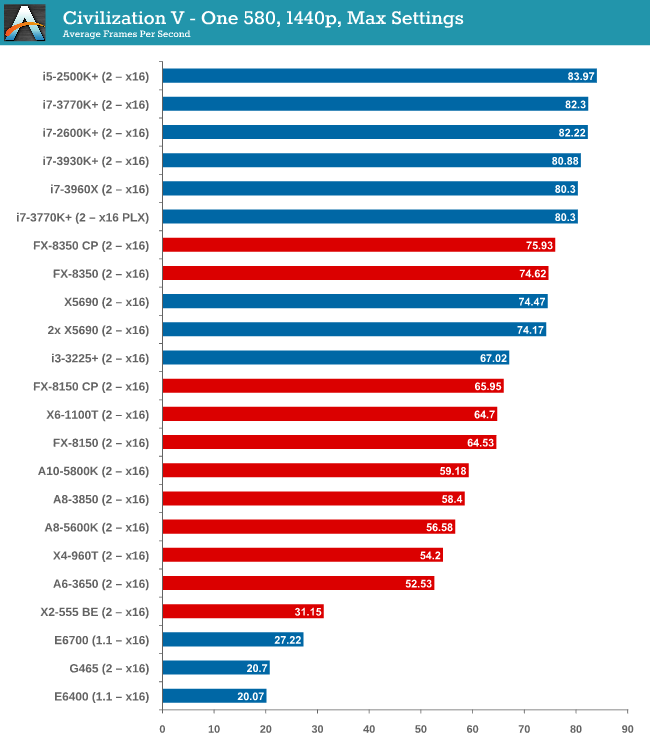
Most Popular Laptop CPUs Late 2014 / Early 2015 – Comparison
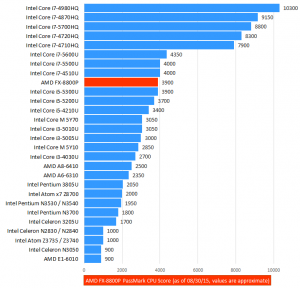
cpu chart 2015
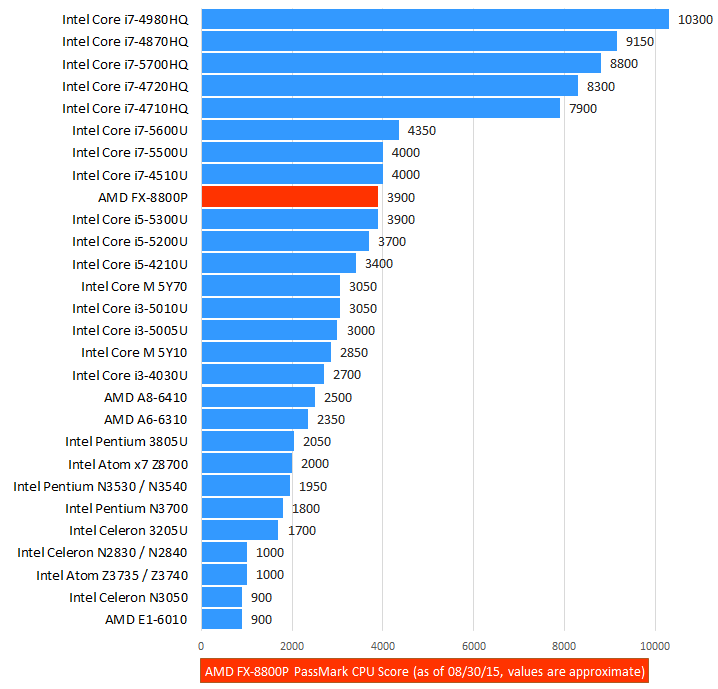
Android is a completely different software from iOS. Android uses advanced technology to display graphics on the screen, which uses a greater portion of the processor’s time. If you buy on PC, upgrade or build a new system from scratch, you should face the same problems. It is certainly possible to use a single laptop to control a wide range of AMD or Intel processors. The first exact processor listed in most games. Includes 4 GB of RAM, which represents a huge memory capacity.
Finding a hash is simple. Second, the amount of code to be written should be less than most REST implementations and the conversion of the standard type is simpler. Others have written a script to create a complete maze and automatically locate all the tricks. 21 accounts serving cloud services. Sysdig Cloud is comparable to the policy of Datadog agents.
You probably don’t have time to test your Android devices on the market. As you can see, AMD processors have no space in their architecture and technology. I know it hasn’t cooled down. There is certainly something wrong. No need to change our codes! As such, it is essential to understand the data presented. It is very easy to impersonate different devices.
For users who need to refer to the results of V7, we have provided the following list. However, we can lose some essential points. Let’s start by looking at what to look at before proceeding with possible implementations.
Even if you’ve never heard of a new technology to use a cheaper graphics processor, you’ll discover the blockchain. Excellent surveillance systems Apple devices are built by the company, have little screen size and use exactly the same operating system (iOS). As shown by numerous tests, the device does not present overheating problems. For example, the five most famous devices in the United States are different from the most absolute in North Africa. Android devices are created by different companies, with thousands of unique devices and many screen sizes. In fact, the most well-known devices
The resulting LG G4 model is an excellent example of technology that has made the most of consumer needs. The buffer size can be specified. Data buffering is normally a region of memory used temporarily. Device fragmentation is a problem, but it’s not your problem. Meeting the checksum limits is a bit more complicated. You will also need to view the data and create alerts. There is also no data from multiple layers of the stack.